本文最后更新于 2024年8月23日 下午
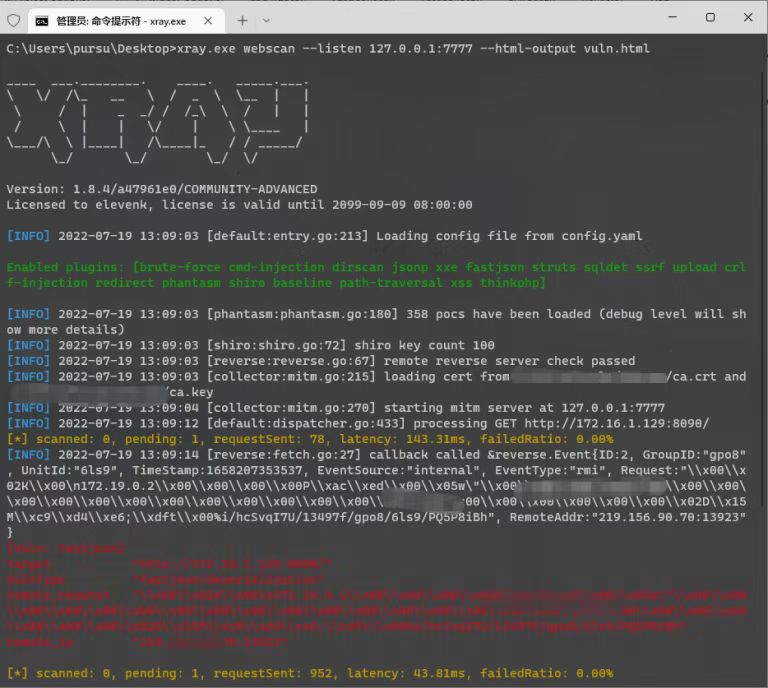
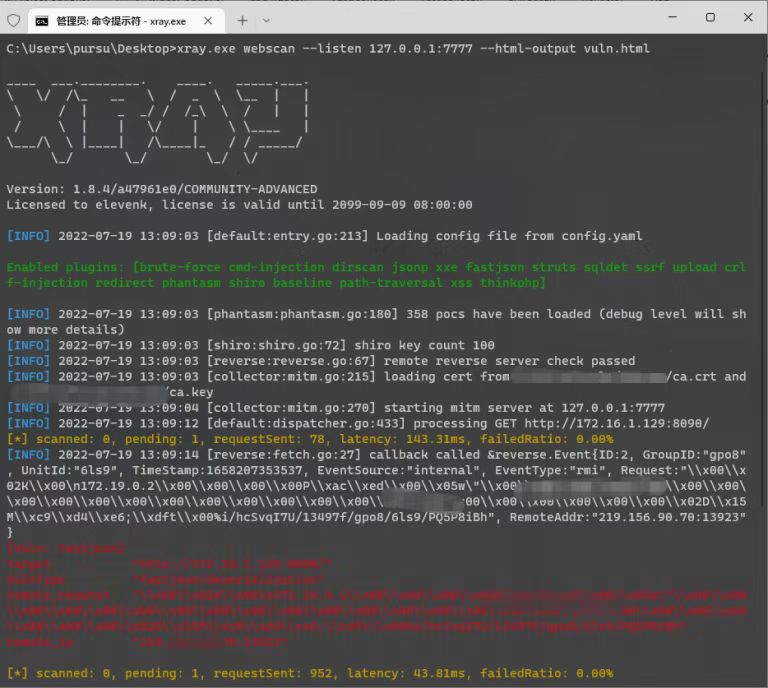
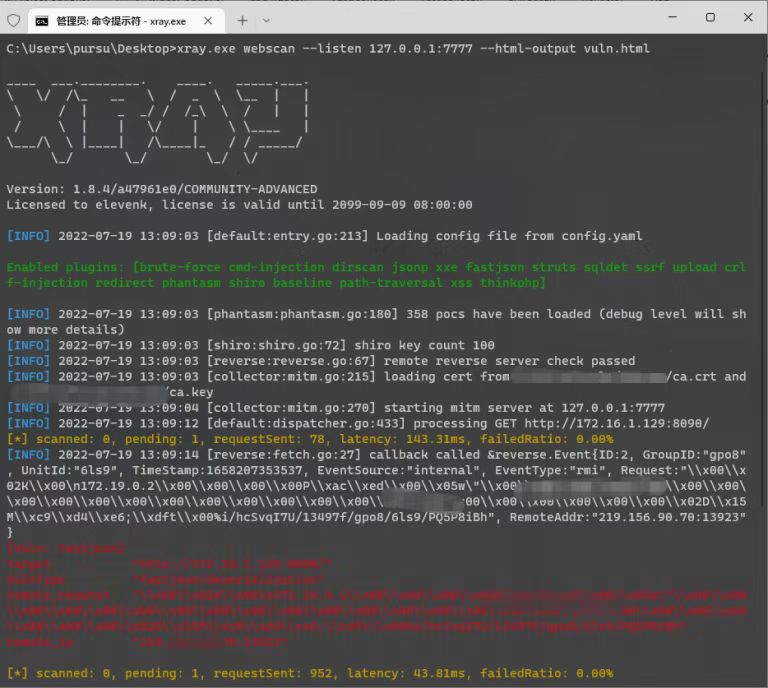
1、被动扫描
1
| xray.exe webscan --listen 127.0.0.1:7777 --html-output vuln.html
|
2、xray配置
服务端配置(config.yaml)
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
| reverse:
db_file_path: "reverse.db"
token: "password"
http:
enabled: true
listen_ip: 0.0.0.0
listen_port: "8001"
ip_header: ""
dns:
enabled: true
listen_ip: 0.0.0.0
domain: "xxx.com"
is_domain_name_server: false
resolve:
- type: A
record: ns1
value: 121.4.x.x
ttl: 60
client:
remote_server: false
http_base_url: ""
dns_server_ip: ""
|
客户端配置(config.yaml)
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
| reverse:
db_file_path: ""
token: "password"
http:
enabled: false
listen_ip: 0.0.0.0
listen_port: ""
ip_header: ""
dns:
enabled: false
listen_ip: 0.0.0.0
domain: ""
is_domain_name_server: false
resolve:
- type: A
record: localhost
value: 127.0.0.1
ttl: 60
client:
remote_server: true
http_base_url: "http://121.4.x.x:8001"
dns_server_ip: "121.4.x.x"
|
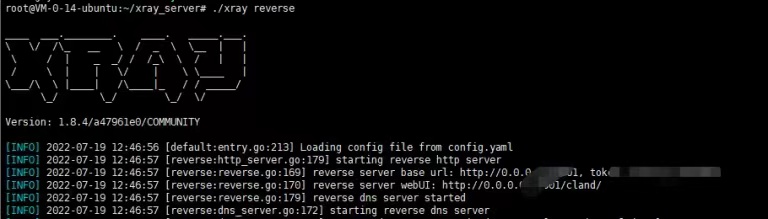
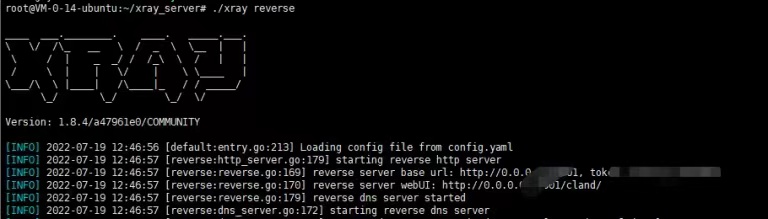
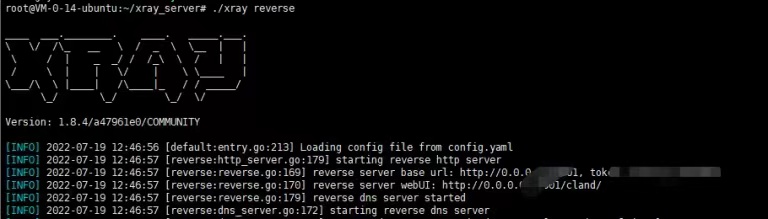
3、服务端开启
1
2
3
| ./xray reverse
nohup ./xray reverse >/dev/null 2>&1 &
|
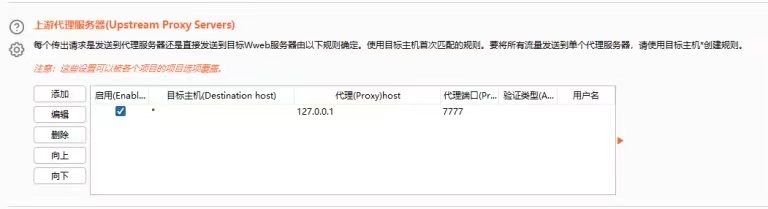
4、Fastjson漏洞测试
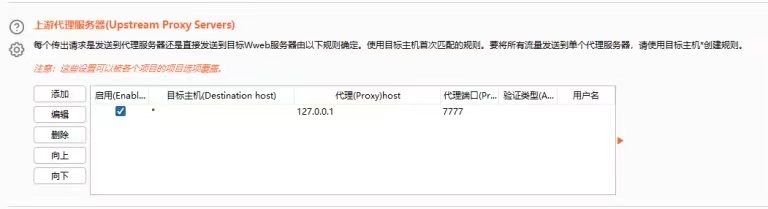
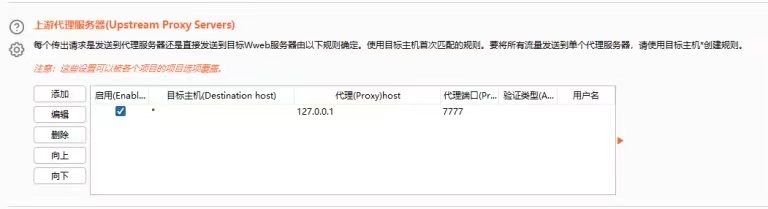
burpsuite转发流量到127.0.0.1:7777,xray开启被动扫描